Estimated reading time: 2 minutes
Table of contents
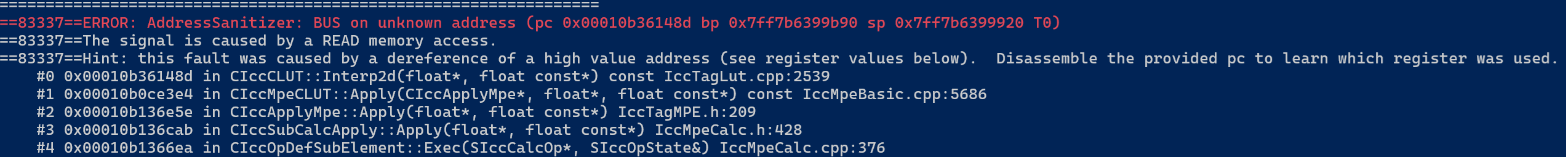
tl;dr: Color Profile Injection is due to untrusted inputs within color profile blobs.
Why? Color profiles rely on offset and length fields, enabling crafted profile data to corrupt neighboring structures.

Color Profile Injection Background
Color Profile Injection (CPI) occurs because user-controllable inputs can corrupt a color profile binary layout.
Resulting impact includes memory corruption, logic bypasses, and potential code execution.
Profile Injection Defense in Depth
- Do not construct color profiles using string or byte concatenation.
- Check all user-controlled data that influences color profile content:
- Check & enforce fixed lengths
- Reject unexpected or unexpected binary data
- Make sure user input can’t affect offsets, tag counts, or size fields
Ineffective or Insufficient Input Sanitization
These controls are commonly used but are not sufficient:
- Escaping or limiting text input
Color profiles are binary formats; character-based sanitization does not prevent binary structure changes. - Trusting earlier data (second-order injection)
Color profile data that passes validation at creation time later be reprocessed. Different components can have different parsing assumptions. - Only using third-party libraries is not enough.
Libraries do not prevent injection when user input is allowed to influence structural fields such as offsets or lengths.
CWE References
- CWE-20 – Improper Input Validation
https://cwe.mitre.org/data/definitions/20.html - CWE-119 – Improper Restriction of Operations within the Bounds of a Memory Buffer
https://cwe.mitre.org/data/definitions/119.html - CWE-707 – Improper Neutralization
https://cwe.mitre.org/data/definitions/707.html
Knowledgebase
- https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-26730
- https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2023-32443
- https://bugs.chromium.org/p/project-zero/issues/detail?id=2226
- https://nvd.nist.gov/vuln/detail/CVE-2022-26730
- https://nvd.nist.gov/vuln/detail/CVE-2023-32443

You must be logged in to post a comment.