Estimated reading time: 6 minutes
Executive Summary
This Article will guide you through SRD First Boot and cryptex installation to Quickstart your Research by Building from Source or Installing from pre-built DMG.
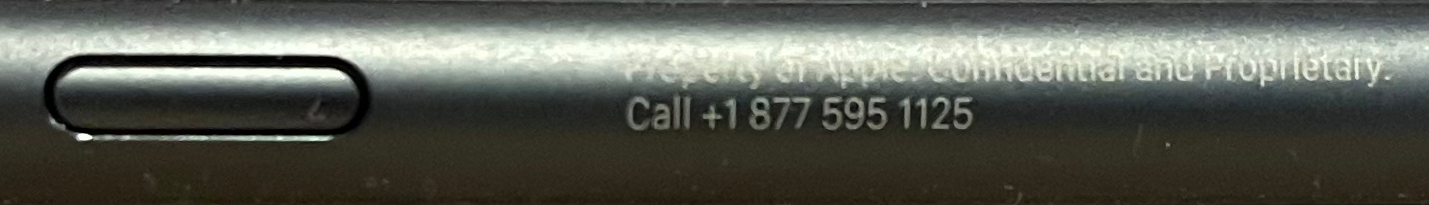
I am David Hoyt. I was a participant in the Apple Security Research Device Program for 2021 & 2022. Apple provided 2 SRD Devices, iPhone 11 & iPhone 12, to conduct A/B Testing which was very helpful for Security Research.
Table of contents
Gallery of Pictures | Circa 2023 | iPhone 11 & 12 SRD’s
Prerequisites
- macOS
- Xcode Beta
- Security Research Tools
- brew install gnu-sed automake
SRD First Boot
This Post will cover Connecting your Apple Security Research Device (SRD) to an X86_64 or M1 for installation of a cryptex using a Host. Topics covered are First Boot, Configuration Options, Prebuilt Binaries, Cryptex File System Installation and Code Signing.
Install Steps
This example makes use of the directory ../example-cryptex/.








- Plug in your SRD to your X86_64 or M1 HOST
- Open Finder and Trust the Device
- On the SRD Screen, Trust the Host
- Open Terminal
- cd example-cryptex
Read this Article before you type:
makeFirst Boot
Boot your Apple SRD and complete the usual Retail Setup taking care to observe the remarks below. Welcome to the Fold!

DO NOT USE YOUR ICLOUD DEVELOPER ACCOUNT
DO NOT ENTER ANY iCloud, Password, PIN or Recovery Number
ONLY Wireless Network Info

DO NOT ATTEMPT to Upgrade the SRD via Retail Methods like me…

First Boot: Plug in to Host and Boot the SRD. Step thru the configuration screens taking care to Bypass the iCloud, Password, PIN and Recovery Number. Only input your Wireless Info. Open Safari and check that you can Surf the Web. Next, it is time to attach the SRD to a Host.
Cryptex Install
Read my next Article for how to Install a Cryptex to the SRD or Install the pre-built example SRD Cryptex DMG with the Link below. My SRD Repo is helpful with pre-built binaries and deep dive technical data.
Install Example SRD Cryptex DMG
Copy and Paste in Terminal to Download and Install an example SRD DMG
/bin/bash -c "$(curl -fsSL https://raw.githubusercontent.com/xsscx/srd/main/dmg/install.sh)"Scripted
cd example-cryptex
wget https://xss.cx/srd/dmg/srd-universal-cryptex.dmg
cryptexctl ${CRYPTEXCTL_FLAGS} create --research --replace ${CRYPTEXCTL_CREATE_FLAGS} --identifier=com.example.cryptex --version=1.3.3.7 --variant=research srd-universal-cryptex.dmg
cryptexctl ${CRYPTEXCTL_PERSONALIZE_FLAGS} personalize --replace --variant=research com.example.cryptex.cxbd
cryptexctl uninstall com.example.cryptex
cryptexctl install --variant=research --persist com.example.cryptex.cxbd.signed
cryptexctl listYou now have a fresh cryptex installed on your SRD with debugserver and frida. Create a Custom Kernel Cache to increase introspection and read some of the later Issues I encountered during 2022.
Video
Resources
Source: https://github.com/apple/security-research-device/tree/main/example-cryptex
- PR42: https://github.com/apple/security-research-device/pull/42
- Universal DMG: https://xss.cx/srd/dmg/srd-universal-cryptex.dmg
- ASAN Beta DMG: https://xss.cx/srd/dmg/srd-asan-cryptex-beta.dmg
- UBSAN Beta DMG: https://xss.cx/srd/dmg/srd-ubsan-cryptex-beta.dmg
- Install: https://github.com/xsscx/srd/tree/main/dmg#readme
- Discussion: nvram settings disabling KTRR, CTRR and kASLR https://github.com/apple/security-research-device/discussions/2
- Build Entitlements Issues for PR 42, 48, 49 https://github.com/xsscx/srd/blob/main/srd_tools-24.100.3/example-cryptex/srd-iphone11-iphone12-entitlements-testing-sample-example.md
Workbench
What is an example Work Bench Configuration?
M1 & X86 Mini’s and more powerful PC hardware, JTAG Cables and typical debugging hardware found in a Lab.
Some of the essential Debugging Tools on the workbench are: M1 Mini, X86_64 Pro Laptop, Jailbroken iPhone X, Frida, Wifi-Pineapple, Monitor/Inject Network Cards, Hardware Taps, Hopper, IDA, Breakout Boards, RasPi’s, SIM Cards, POTS Line, Class 5 Switch Access, Twilio, EMF Gear, Thermal Devices, RF/RFI/SDR Tooling. An iPhone 12 Pro, iPad Pro, Homepod & Watch and other Accessories have been very helpful too.
Some of the essential Software Debugging Tools are: Toybox Unstripped, Burp Suite Pro, Proxyman, Wireshark, Paw Cloud, DNS Server, Aircrack-ng, OpenPCAP, Replay Tools, a Cloud Platform for CI/CD, Telemetry, Fuzzing, Crash Reporting and more.
Related Content
This Article will guide you through SRD First Boot and cryptex installation to Quickstart your Research by Building from Source or Installing from pre-built DMG.
Tweet

7 responses to “SRD First Boot”
[…] Kalman’s post on Tuesday, it appears that there was only one blog post that showed pictures of a Security Research Device, published in […]
[…] Kalman’s post on Tuesday, it appears that there was only one blog post that showed pictures of a Security Research Device, published in […]
[…] even more interesting? This particular blog post that mostly when unnoticed before TC highlighted it today. Want to join on the bug hunting fun? […]
[…] a blog post brought to light by TC, Apple is open to researchers with a proven track record of finding security […]
[…] even more interesting? This particular blog post that mostly when unnoticed before TC highlighted it today. Want to join on the bug hunting fun? […]
[…] than Kalman’s put up on Tuesday, it seems that there was only one blog post that confirmed footage of a Safety Analysis System, revealed in […]
[…] Kalman’s post on Tuesday, it appears that there was only one blog post that showed pictures of a Security Research Device, published in […]