Category: Apple
-
CVE-2023-32443 | sips | Color Bleed
CVE-2023-32443 | sips | Processing a file may lead to a denial-of-service or potentially disclose memory contents.
-
CVE-2022-26730 | Profile Bleed

Profile| Processing a maliciously crafted image may lead to arbitrary code execution.
-
SRD Picture Gallery

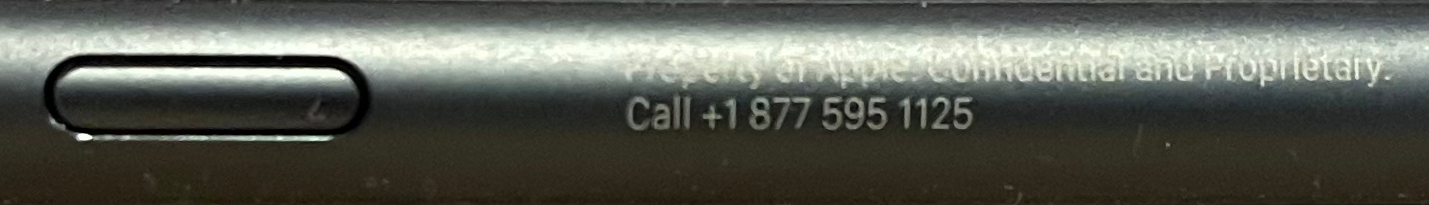
The SRD Picture Gallery is Published by David Hoyt. I was a participant in the Apple SRD Program in 2021 & 2022.
-
Best Practice & Transparency

This Article by David Hoyt looks at Chilling Effect, Best Practice & Transparency in the IT Security Sector.
-
Introspection Claim

Rebuttal by David Hoyt of Apple SRD Cohort to Apple vice president Craig Federighi with respect to public statements made in Wall Street Journal Article.
-
missing dylib libMobileRestoreInternalExtensions

SUMMARY: Failed iOS Upgrade on SRD due to Missing Dylib in SecurityResearchTools_20C80 with Dylib Injection PoC
-
srdutil

The srdutil utility is used to Checkin your Device with Apple Corporation. Every 2 weeks set a cron job to checkin your SRD with the Mothership.
-
SRD First Boot
This article provides a guide for SRD First Boot and cryptex installation, as well as insights from the author’s experience in the Apple Security Research Device Program. It includes installation prerequisites, detailed steps for first boot and cryptex installation, and a discussion on workbench configurations and essential debugging tools. References to relevant resources and repositories…
-
XNU Crash Analysis

This Article is intended for quick assessment of XNU Crash Analysis. Manually debugging the Code is the only way to be sure something is or isn’t exploitable. A Crash is only a security issue if it is triggered by untrusted input.


You must be logged in to post a comment.